Recognizing that each organization or department faces distinctive threats, ─ X•Aware offers both Signal Monitoring and Identifier Sensor Systems to ensure continuous counter-surveillance coverage.
Operating continuously, autonomously, and remotely.
X•Aware Sensor Systems are easily deployable in concealed locations such as ceiling spaces, electrical enclosures, or custom-designed housings — allowing seamless integration into the client’s office layout.
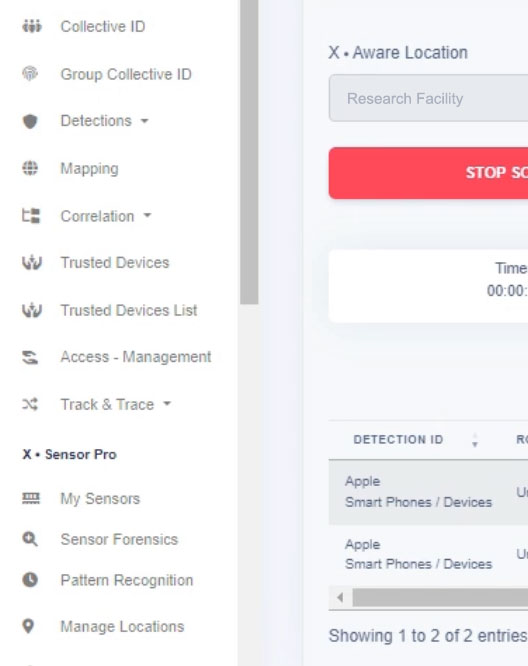
Another advantage is that the AI-powered X•Aware Dashboard, with its intelligent visual and alerting capabilities, can be delivered as a customizable framework tailored to the client’s user experience requirements.
X•Aware enables its TSCM partners to deliver autonomous and continuous TSCM technology, fully customized to the client’s needs — supported by a highly modular system design.
The Signal Monitor Sensor System allows rapid switching between frequencies and bandwidths, enabling seamless scanning across cellular and other pre-selected data-transmitting frequencies.
Additionally, the Signal Monitor Sensor System can be extended with multiple SDRs operating from 50 MHz to 6,000 MHz, enabling simultaneous monitoring of pre-selected frequencies.
Equipped with on-site and remote baseline scan capabilities, the system allows thresholds to be set for automated alerts — including those based on pattern recognition scenarios.


Whether the use case is to detect and identify Wi-Fi, BLE, IoT, or Cellular devices — with the ability to whitelist, blacklist, or track them — each Identifier Sensor System can be fully customized to meet the client’s requirements.
The Device Identifier Sensor System supports hopping between 2G+3G and/or 4G+5G Cellular Frequencies and can be extended with fixed Wi-Fi, BLE, and IoT adapters.
Additionally, the Device Identifier Sensor System can be extended with multiple SDRs operating simultaneously across all pre-configured cellular frequencies. It is also fully extendable with Wi-Fi, BLE, and IoT detection capabilities.
Interested to learn more?
X•Aware
Providing Awareness & Assurance Against Invisible Threats
Designed in the Netherlands